Software patches are small, targeted changes to software that fix vulnerabilities, improve performance, or add compatibility, and they form a foundational element of modern security hygiene. In a modern IT environment, effective patch management coordinates discovery, verification, and timely delivery of these updates across endpoints, servers, network devices, and cloud services, reducing drift. Regular software updates and security updates reduce exposure, while vulnerability remediation closes gaps attackers could exploit, helping maintain regulatory compliance and operational resilience amid evolving threats. Organizations rely on automated scanning, testing, and deployment to ensure patches are applied consistently, minimize downtime, and document outcomes for audit trails and performance monitoring, integrating software patching into routine governance. By prioritizing patching decisions, communicating risk, and aligning with governance frameworks, teams can strengthen defenses and keep systems running smoothly in diverse environments.
Viewed through the lens of ongoing software maintenance, patching becomes a disciplined routine of vulnerability fixes, update cadences, and guarded deployment pipelines. Rather than using patches alone, teams describe maintenance releases, hotfixes, and security updates that shore up code and minimize risk. This latent semantic indexing approach ties together ideas such as vulnerability remediation, software updates, patch management, and software patching to boost relevance for readers and search engines.
Patch Management Best Practices: Strengthening Security with Timely Software Updates
Effective patch management is the backbone of a secure IT environment. By continuously identifying, acquiring, testing, and deploying patches, organizations gain visibility into their software footprint and can prioritize remediation based on risk. This approach aligns with incident response, change control, and IT service management, ensuring that security updates and software updates are applied in a coordinated, auditable manner.
A mature patch management program reduces exposure to CVEs and helps maintain regulatory compliance. With a clear rollout plan, defined maintenance windows, and rollback options, teams can minimize disruption while closing known vulnerabilities. In short, patch management is a proactive discipline that blends threat intelligence with operational discipline to sustain a stronger security posture.
What Are Software Patches? From Hotfixes to Major Updates
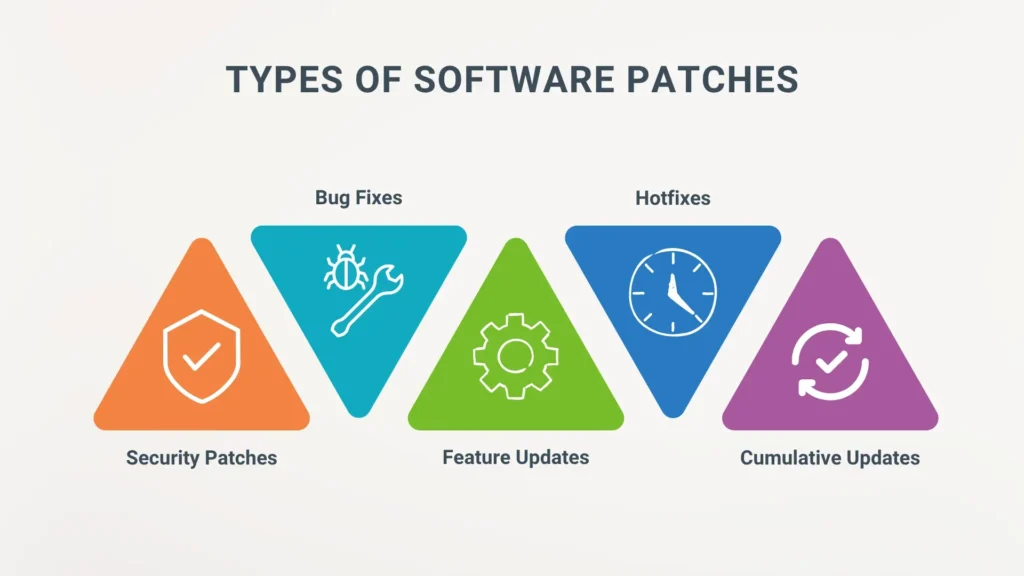
A software patch is a targeted update designed to fix bugs, close vulnerabilities, or enhance functionality. Patches come in various formats, from hotfixes released to address critical vulnerabilities to minor patches that fix a handful of issues and major patches that introduce new features. This spectrum is a core part of software patching, ensuring that software behaves as intended and remains resilient against threats.
Patches play a central role in vulnerability remediation and overall software hygiene. By timely applying these updates, organizations reduce the window of opportunity for attackers who exploit unpatched software, while preserving compatibility with existing workflows and integrations. The practice of software patching therefore supports both security updates and routine software updates that keep systems aligned with current standards.
Security Updates and Vulnerability Remediation: Reducing the Attack Surface with Patches
Security updates are time-sensitive patches designed to neutralize newly disclosed weaknesses. When vendors release a fix, applying it promptly can dramatically shrink the attack surface and lower the risk of data breaches, ransomware, and credential theft. This is why vulnerability remediation through rapid patching is a cornerstone of defensive cybersecurity.
Integrated with patch management, security updates become part of a repeatable workflow that prioritizes high-risk CVEs and critical systems first. Regularly applying these patches not only strengthens protection but also helps organizations demonstrate due diligence in vulnerability remediation and software updates across the enterprise.
End-to-End Patch Deployment: Testing, Rollouts, and Change Control
A robust deployment strategy covers the entire lifecycle from testing to production. Patch testing in a controlled environment helps verify compatibility, minimize downtime, and prevent disruptions to critical applications. A phased rollout, maintenance windows, and clearly defined rollback plans are essential components of successful software updates and patch management.
Automation plays a key role in executing the plan at scale, from detection and download to staging, deployment, and verification. Ongoing verification and post-deployment monitoring ensure patches installed correctly and that any side effects are identified early. This disciplined approach to deployment reinforces patch management best practices and accelerates vulnerability remediation without compromising operations.
Measuring Patch Effectiveness: Metrics for Patch Management and Compliance
Quantifying patch effectiveness involves tracking metrics such as time-to-patch, patch coverage, and post-patch incident rates. Regular audits and reporting help leadership understand risk posture, justify investments in patch management tools, and identify process improvements. These metrics connect security updates and vulnerability remediation outcomes to business risk.
A data-driven view of patching also includes root cause analyses of failed patches and the adoption rate of automated workflows. By continuously monitoring progress, organizations can optimize asset inventory accuracy, prioritization, and testing rigor, ensuring that software patching efforts translate into tangible reductions in exposure and improved compliance with security standards.
Tackling Patch Challenges Across Windows, Linux, Cloud, and IoT Environments
Patch management varies by environment. Windows and Windows Server typically rely on Windows Update or WSUS, while Linux systems use package managers and configuration tools to enforce patch compliance. Cloud and SaaS services push many security updates automatically, but organizations still need visibility into third-party services and container patches.
IoT and embedded devices present unique challenges due to hard-to-reach endpoints and firmware updates. A resilient patch strategy requires asset discovery, robust testing, and scalable rollout plans that account for diverse platforms. By applying consistent patch management practices across all environments, teams can maintain strong vulnerability remediation, minimize downtime, and sustain software updates that keep critical operations secure.
Frequently Asked Questions
How do software patches fit into patch management and why are security updates important?
Software patches are targeted updates that fix vulnerabilities and improve functionality. In patch management, teams identify, test, and deploy these patches across endpoints to reduce risk. Security updates are time-sensitive patches that close CVEs and strengthen defenses, helping organizations stay compliant and secure.
What is the difference between software patches and software updates, and how does vulnerability remediation fit in?
Software patches are specific fixes aimed at addressing defects and vulnerabilities, while software updates may include patches, feature improvements, and bug fixes. Vulnerability remediation is the ongoing effort to address known weaknesses, often achievable through timely security updates and the application of software patches.
How should organizations prioritize patching under patch management to improve vulnerability remediation and ensure timely security updates?
Prioritize based on risk, asset criticality, and CVSS scores; categorize patches into critical security updates, routine updates, and feature patches. Focus remediation on high-risk issues to reduce exposure, and validate patches in a test environment before broad deployment to support vulnerability remediation and timely security updates.
What are best practices for testing and deploying patches to minimize downtime within a patch management program?
Test patches in a staging environment to verify compatibility with critical workflows and integrations. Automate detection, testing, and deployment where possible, establish change control and rollback plans, and schedule maintenance windows with clear communication to minimize business impact.
How can you measure patch effectiveness and patch coverage within patch management to support security updates?
Track metrics such as time-to-patch, patch coverage, and post-patch incidents. Regular audits and reporting help justify investments in patch management tools and personnel, while dashboards monitor remediation effectiveness and guide vulnerability remediation efforts.
What challenges arise when applying software patches across Windows, Linux, cloud services, and IoT devices, and how can patch management address them?
Different environments use different update mechanisms (Windows Update/WSUS, Linux package managers, cloud auto-patching, IoT firmware). Address them with accurate asset inventory, standardized processes, automation, testing, and phased rollouts with rollback plans and monitoring.
| Topic | Key Points |
|---|---|
| What are software patches? |
|
| Why patches matter for security |
|
| Patch management as a discipline |
|
| Key components of a patch management program |
|
| Patch deployment and updates in practice |
|
| Best practices for patching |
|
| Patch management in different environments |
|
| Measuring patch effectiveness |
|
| Common challenges and how to address them |
|
| Future trends in patching and security updates |
|
| Conclusion |
|
Summary
Software patches are essential to security and reliability in modern IT environments. A strong patch management program reduces risk, protects sensitive data, and helps workloads run smoothly. By prioritizing timely security updates, vulnerability remediation, and the broader discipline of software patching, organizations can build a resilient IT posture that adapts to changing threats and technologies. Embracing comprehensive patch management is a foundational practice for sustainable cybersecurity.