Patch lifecycles shape vulnerability patching, software patch management, patch deployment strategies, patch testing and verification, and patch management best practices for modern software. Understanding these lifecycles helps organizations coordinate security with development and operations, reducing risk and improving reliability across applications, containers, and cloud services; this alignment fosters clearer accountability and traceable performance metrics for patch cycles; moreover, it helps prioritize resource allocation, informs service level expectations, and strengthens supplier risk management. By mapping each phase—from discovery and assessment to deployment and verification—teams establish clear ownership, governance, and traceability that support audits and continuous improvement, ensuring that changes are planned, tested, documented, and reversible when necessary, and that security and operations collaborate. A well-structured lifecycle aligns vulnerability management with change control, enabling faster responses to threats and smoother patch deployments across heterogeneous environments, including on-premises data centers and modern multi-cloud architectures, without sacrificing performance or user experience, and with measurable rollbacks if needed. This introductory overview sets the stage for practical steps, and points readers toward best practices that balance speed, safety, and system performance, providing a foundation for deeper discussions on automation, metrics, governance, and ongoing risk management for sustained improvement.
Patch lifecycles: From vulnerability discovery to production verification
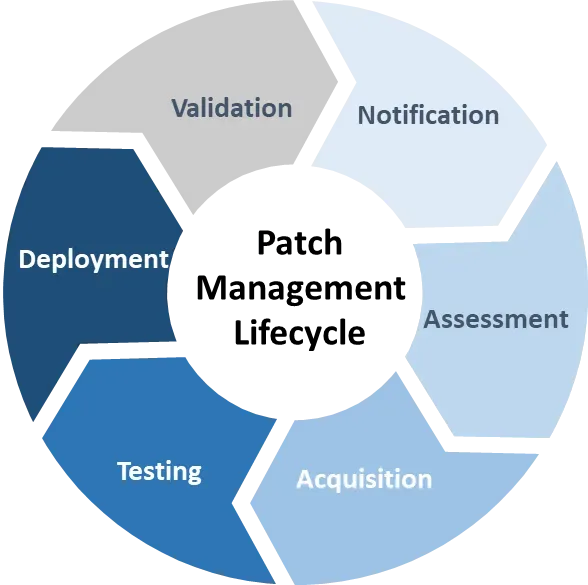
Patch lifecycles guide organizations from the moment a vulnerability is identified to the point where the fix is deployed, validated, and verified in production. This journey sits at the heart of vulnerability patching and the broader practice of software patch management, ensuring security is tightly integrated with service delivery and reliability.
By following an end-to-end sequence that covers discovery, assessment, development, deployment, and validation, teams can balance speed with safety. Implementing patch deployment strategies and adhering to patch management best practices helps reduce risk, minimize downtime, and maintain customer trust through auditable, repeatable processes.
Discovery and assessment: Building a solid base for vulnerability patching and software patch management
A robust discovery phase starts with a comprehensive asset inventory, continuous vulnerability scanning, and a structured risk assessment. This foundation ensures visibility into what needs patching and enables targeted vulnerability patching within a broader software patch management program.
Understanding dependencies across platforms, libraries, and services is essential. Cross-functional collaboration between security, IT operations, and development teams helps map patch requirements to business services and create a prioritized backlog that guides remediation efforts.
Development and verification: Vetting patches through rigorous patch testing and verification
Patches originate from vendors, open-source maintainers, or internal mitigations, and must be acquired, validated, and prepared for deployment. The development and verification stage focuses on ensuring fixes address the reported vulnerability without introducing new issues.
Patch testing and verification occur in lab or staging environments that mirror production as closely as possible. This helps catch regressions, assess compatibility with operating systems and security controls, and determine realistic deployment outcomes, all while documenting the rationale and success criteria.
Deployment strategies: Structured rollout with phased and automated patch deployment strategies
Deployment strategies guide how patches move from test environments into production. Phased rollouts, canary releases, blue-green deployments, and automated pipelines minimize risk by validating impact on small groups before broader dissemination.
Careful planning around maintenance windows, stakeholder communications, and rollback readiness is essential. Automation—from configuration management tools to deployment pipelines—enables consistent, scalable patch deployment across endpoints, servers, and containers while preserving stability.
Validation and monitoring: Real-time oversight of patch effectiveness and performance
After deployment, validation checks confirm correct installation, service availability, and expected behavior. Validation activities include verifying patch versions on affected systems and monitoring for anomalies such as performance regressions or application errors.
Ongoing monitoring provides continuous visibility into patch coverage, compliance status, and remediation timelines. Real-time dashboards and alerting support rapid triage, remediation, and adjustments to patch management processes as threats and environments evolve.
Governance, compliance, and documentation: Aligning patch lifecycles with policy and audits
Governance and documentation ensure patch activities align with policy, regulatory requirements, and audit expectations. Keeping patch records, test results, deployment notes, and rollback histories supports transparency and accountability across the organization.
Integrating patch management with software development lifecycles, CI/CD workflows, and incident response playbooks embodies patch management best practices. Regular policy reviews and scalable processes help sustain security, compliance, and operational resilience over time.
Frequently Asked Questions
What are patch lifecycles and how does vulnerability patching fit within them?
Patch lifecycles map a fix from discovery to deployment and verification. Vulnerability patching is the core trigger, guiding the lifecycle through discovery and assessment, development and verification, deployment, validation, and governance to ensure a secure, auditable remediation.
How do patch management best practices shape the patch lifecycles process?
Patch management best practices provide governance, automation, and documentation that ensure consistent handling across all phases of the patch lifecycles— from discovery to rollback. They emphasize repeatability, risk-based prioritization, and clear ownership to reduce exposure and improve compliance.
What role do patch deployment strategies play in the patch lifecycles?
Patch deployment strategies such as phased rollouts, canary releases, and blue-green deployments are central to the deployment phase of the patch lifecycles. They balance speed with safety, enabling quick remediation while minimizing disruption and allowing rapid rollback if issues arise.
Why is patch testing and verification essential in the patch lifecycles?
Patch testing and verification are critical to confirm that fixes actually mitigate the vulnerability without causing regressions. Testing in a production-macing staging environment validates compatibility, performance, and security controls before full deployment within the patch lifecycles.
How does vulnerability patching influence discovery and assessment in patch lifecycles?
Vulnerability patching drives the discovery and assessment phase, where asset inventories and vulnerability scans identify what needs patching, and risk scoring prioritizes actions. This informs the patch lifecycles backlog, owner assignments, timelines, and rollback plans.
What common pitfalls derail patch lifecycles and how can organizations address them with patch management best practices?
Common pitfalls include poor visibility, rushed patches, and fragmented tooling. Address them with automation, integrated monitoring and ticketing, clear governance, and continuous improvement aligned with patch management best practices to keep the lifecycle secure and auditable.
| Aspect | What It Covers | Key Outcomes |
|---|---|---|
| Phase 1 — Discovery and Assessment | Asset inventory, vulnerability scanning, risk assessment, and dependency mapping; prioritize patches; establish a backlog with owners, timelines, and rollback plans | Clear visibility into what needs patching; prioritized backlog; alignment with business services; reduced risk |
| Phase 2 — Patch Development and Verification | Sources include vendor advisories, open-source maintainers, and internal mitigations; acquire, validate, and prepare patches; test for compatibility; verify mitigation in lab/staging; pilot deployments; finalize approvals, rollback procedures; document rationale and validation; internal patches for zero-days | Reduced regression risk; validated fixes; governance and readiness for deployment; traceable decisions and validation criteria |
| Phase 3 — Deployment and Rollout | Deployment strategies (phased, canary, blue-green); maintenance windows; clear stakeholder communication; rollback readiness; automation via CM tools and pipelines; balance speed with safety | Minimized risk to large user bases; smoother adoption; faster, but safer, remediation; consistent patch application across endpoints |
| Phase 4 — Validation and Monitoring | Verify patch versions on endpoints; confirm service availability; monitor for anomalies; use dashboards for real-time patch coverage and remediation timelines; continuous monitoring and rapid triage plan | Assurance of successful installation; early detection of issues; ongoing visibility into security and performance post-patch |
| Phase 5 — Governance, Compliance, and Documentation | Policy, regulatory and audit alignment; preserve patch records, test results, deployment notes, approvals, and rollback histories; integrate with CI/CD workflows; regular policy reviews | Compliance readiness; auditable, repeatable process; reduced governance risk; improved alignment with development and operations |
| Common Pitfalls and How to Avoid Them | Inadequate visibility; rushing patches; poor change management; overreliance on manual processes; fragmented tooling | Automated discovery and reconciliation; balance urgency with testing and rollback; enforce approvals and documentation; invest in integrated tooling |
| Why Patch Lifecycles Matter | Not just quick patching but a repeatable, auditable process that integrates security with operations | Reduces risk, improves stability, enhances compliance, enables faster threat responses |
| Case in Point | Illustrates end-to-end lifecycle in action with discovery, prioritization, staged deployment, monitoring, and full documentation | Demonstrates a repeatable, auditable process that achieves compliant, secure patch delivery |
Summary
Conclusion: Patch lifecycles describe the end-to-end process of identifying, developing, deploying, validating, and governing patches to keep software secure and reliable. By starting with discovery and assessment, moving through careful development and testing, executing disciplined deployments, and maintaining ongoing validation and governance, organizations close the loop between threat discovery and safe production operation. The disciplined lifecycle yields reduced risk, greater stability, improved regulatory compliance, and faster responses to new vulnerabilities. Key practices include maintaining asset inventories, employing risk-based prioritization, automating where possible, and documenting decisions and rollbacks. Embracing patch lifecycles as a repeatable capability ensures security and operational excellence as technology and threats evolve.